Validation checkpoints are the guardians of quality assurance, yet many teams unknowingly skip critical testing phases that could prevent catastrophic failures in production environments.
🎯 The Real Cost of Incomplete Validation Testing
When software reaches end users with undetected flaws, the consequences extend far beyond simple bug fixes. Organizations face reputation damage, revenue loss, and user trust erosion that can take months or years to rebuild. Despite best intentions, many development teams fall into validation traps that leave significant gaps in their testing coverage.
The validation checkpoint framework serves as a systematic approach to ensuring every component, integration point, and user interaction receives appropriate scrutiny before deployment. However, the complexity of modern applications—with their microservices architectures, third-party integrations, and diverse deployment environments—creates numerous blind spots where incomplete testing thrives.
Understanding where validation failures commonly occur represents the first step toward building robust testing protocols. Research indicates that approximately 68% of production issues stem from scenarios that were never explicitly tested during the quality assurance phase, revealing a fundamental disconnect between testing strategies and real-world usage patterns.
🔍 Hidden Pitfalls That Compromise Testing Integrity
The most dangerous validation gaps are those that remain invisible until after deployment. Teams often believe they’ve conducted thorough testing when, in reality, they’ve only examined the happy path scenarios while neglecting edge cases and integration complexities.
The Happy Path Illusion
Testing teams naturally gravitate toward ideal scenarios where everything functions as designed. Users enter correct information, systems respond promptly, and data flows seamlessly through integration points. This happy path testing creates a false sense of security while leaving critical failure modes unexplored.
Real-world applications must handle malformed inputs, network interruptions, concurrent user actions, and unexpected data states. When validation checkpoints focus exclusively on optimal conditions, they miss the scenarios that most frequently cause production incidents.
Integration Point Blindness
Modern applications rarely exist in isolation. They communicate with databases, third-party APIs, authentication services, payment processors, and countless other external systems. Each integration point represents a potential failure vector that demands dedicated validation attention.
Many teams test their application components thoroughly but fail to validate behavior when external systems respond slowly, return unexpected data formats, or become temporarily unavailable. These integration scenarios require specific checkpoint validation strategies that simulate real-world service degradation patterns.
Environment Parity Gaps
The classic “it works on my machine” problem extends beyond individual developer environments to encompass the entire testing ecosystem. Applications tested exclusively in development or staging environments may behave completely differently in production due to configuration differences, resource constraints, or network topology variations.
Validation checkpoints must account for environment-specific factors including database connection pooling, caching behavior, content delivery network interactions, and infrastructure scaling characteristics that only manifest under production-like conditions.
🛠️ Building Comprehensive Validation Frameworks
Effective validation checkpoint implementation requires structured approaches that systematically address testing gaps while remaining practical for real-world development timelines and resource constraints.
The Checkpoint Matrix Approach
Creating a validation matrix helps teams visualize testing coverage across multiple dimensions. This framework organizes validation checkpoints by component, environment, scenario type, and criticality level, revealing gaps that might otherwise remain hidden.
The matrix approach transforms validation from an ad-hoc activity into a systematic process where each checkpoint receives explicit attention. Teams can track which scenarios have been validated, which remain untested, and where additional coverage would provide the greatest risk reduction.
Layered Validation Strategies
Comprehensive validation employs multiple checkpoint layers, each addressing different aspects of application quality. Unit tests validate individual component behavior, integration tests verify communication between modules, system tests examine end-to-end workflows, and acceptance tests confirm business requirement satisfaction.
Many teams implement some validation layers while neglecting others, creating gaps where issues slip through. A complete validation framework ensures appropriate checkpoint coverage at each layer, with clear criteria for determining when validation passes or fails at each level.
Scenario-Based Checkpoint Design
Rather than testing features in isolation, scenario-based validation examines complete user journeys and business workflows. This approach uncovers issues that only appear when multiple features interact or when users follow specific paths through the application.
Scenario checkpoints should include both common usage patterns and edge cases that stress system boundaries. For e-commerce applications, this means validating not just successful purchases but also abandoned carts, payment failures, inventory conflicts, and concurrent checkout attempts.
⚡ Automating Validation Without Losing Depth
Test automation accelerates validation checkpoint execution, but automated testing can create its own blind spots when teams confuse speed with thoroughness. The goal isn’t simply to run tests faster but to expand validation coverage while maintaining quality.
Strategic Automation Prioritization
Not every validation checkpoint benefits equally from automation. Repetitive regression tests, data validation routines, and integration health checks represent excellent automation candidates. Exploratory testing, usability validation, and creative edge case discovery often require human insight and intuition.
Teams should prioritize automation for checkpoints that need frequent execution, have clear pass-fail criteria, and address stable functionality. This strategic approach maximizes automation benefits while preserving resources for validation activities that demand human expertise.
Continuous Validation Integration
Modern development workflows demand validation checkpoints that execute continuously throughout the development lifecycle. Waiting until formal testing phases to validate functionality creates delays and increases fix costs when issues surface late in the development cycle.
Continuous integration pipelines should incorporate progressive validation checkpoints that provide immediate feedback when code changes introduce problems. This shift-left approach catches issues when they’re easiest to fix while maintaining development velocity.
📊 Metrics That Reveal Validation Effectiveness
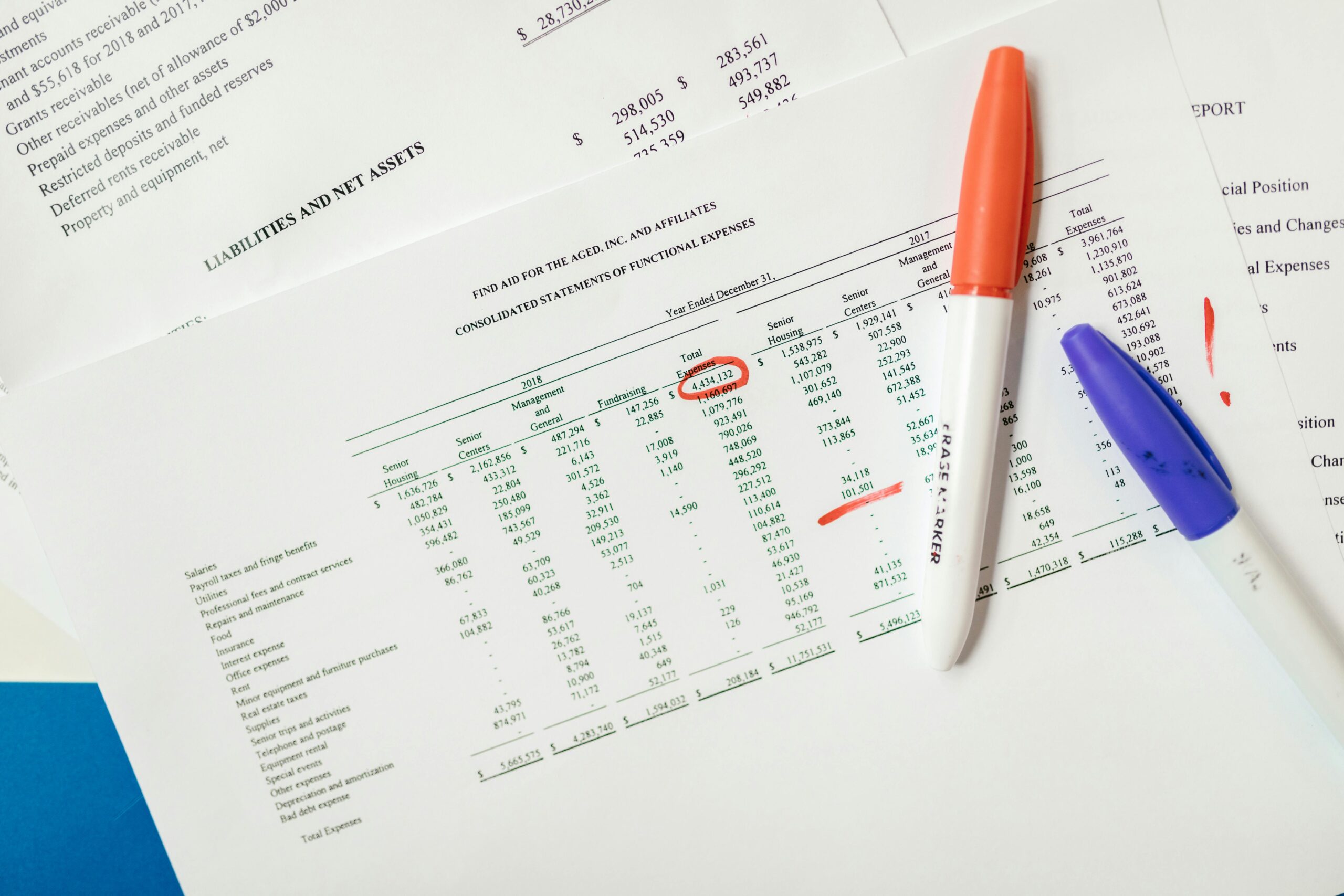
Measuring validation checkpoint effectiveness helps teams identify improvement opportunities and demonstrate quality assurance value. However, selecting appropriate metrics requires understanding which measurements actually correlate with real-world quality outcomes.
Coverage Metrics Beyond Code Percentages
Code coverage percentages indicate which lines execute during tests but reveal nothing about validation quality or scenario completeness. A test suite might achieve 90% code coverage while missing critical business logic validation or failing to test essential user workflows.
More meaningful metrics examine requirement coverage, scenario coverage, integration point validation, and defect escape rates that measure how many issues reach production despite validation efforts. These metrics provide actionable insights into validation checkpoint effectiveness.
Defect Detection Timing
Tracking when defects are discovered reveals whether validation checkpoints function as intended. Issues detected during initial development indicate effective early validation, while production defects suggest checkpoint gaps that allowed problems to escape detection.
Analyzing defect discovery patterns helps teams identify which validation layers need strengthening and which checkpoint strategies effectively catch issues before they reach users. This data-driven approach targets improvement efforts where they’ll have the greatest impact.
🎭 The Human Element in Validation Excellence
While frameworks, automation, and metrics provide structure, validation effectiveness ultimately depends on the skills, mindset, and creativity of testing professionals. Technical checkpoints catch technical issues, but human testers discover the unexpected problems that automated systems miss.
Cultivating the Testing Mindset
Effective validation requires thinking like users who don’t understand system constraints, like attackers seeking vulnerabilities, and like business stakeholders focused on value delivery. This multifaceted perspective helps testers identify validation scenarios that pure technical analysis might overlook.
Teams should encourage creative exploration during validation checkpoint execution, allowing testers to investigate suspicious behaviors and pursue intuitive hunches that might reveal deeper issues. The best validation combines systematic checkpoint execution with exploratory investigation.
Knowledge Sharing and Validation Documentation
Validation knowledge often remains locked in individual tester’s minds rather than being systematically documented and shared. When team members change or time pressures mount, this undocumented knowledge disappears, leaving subsequent validation efforts to rediscover lessons already learned.
Comprehensive validation checkpoint documentation captures not just test procedures but the reasoning behind specific validation approaches, historical issues that motivated particular checkpoints, and insights about where testing gaps commonly appear. This institutional knowledge prevents repeated mistakes and accelerates new team member onboarding.
🚀 Advanced Checkpoint Strategies for Complex Systems
As applications grow in complexity, basic validation approaches become insufficient. Advanced systems demand sophisticated checkpoint strategies that address distributed architectures, asynchronous processing, and emergent behaviors that only appear at scale.
Chaos Engineering for Validation
Deliberately introducing failures during validation reveals how systems respond to adverse conditions. Chaos engineering checkpoints simulate service outages, network partitions, resource exhaustion, and data corruption to verify that applications handle failures gracefully rather than cascading into complete system failures.
This proactive failure injection provides validation insights impossible to obtain through conventional testing. Teams discover whether their error handling actually works, whether fallback mechanisms activate correctly, and whether monitoring systems detect problems as intended.
Performance Validation Checkpoints
Functionality validation means nothing if applications respond too slowly for practical use. Performance checkpoints should validate response times, throughput capacity, resource consumption, and scalability characteristics under realistic load conditions.
Many teams defer performance validation until late in development cycles when addressing discovered issues requires expensive architectural changes. Early performance checkpoints integrated throughout development catch efficiency problems when fixes remain straightforward and inexpensive.
Security Validation Integration
Security cannot be an afterthought tacked onto functional validation. Security checkpoints should validate authentication mechanisms, authorization controls, data encryption, input sanitization, and vulnerability resistance as integral parts of the overall validation framework.
Security validation requires specialized expertise and tools, but basic security checkpoints should exist in every team’s validation framework. These checkpoints catch common vulnerabilities like injection attacks, authentication bypasses, and data exposure issues before they reach production.
🌟 Transforming Validation Culture for Sustainable Excellence
Technical validation frameworks fail without organizational cultures that value thorough testing and provide time for comprehensive checkpoint execution. Sustainable validation excellence requires cultural transformation beyond mere process implementation.
Quality Ownership Across Teams
When quality responsibility rests solely with dedicated testing teams, developers may consider validation someone else’s problem. This separation creates adversarial dynamics where development throws code over walls to testing, who throws defect reports back.
Modern validation excellence requires shared quality ownership where developers implement automated checkpoints, participate in validation planning, and take personal responsibility for ensuring their code passes validation criteria before requesting testing resources.
Balancing Speed and Thoroughness
Business pressures to deliver features quickly can tempt teams to skip validation checkpoints or rush through testing phases. While speed matters, the costs of production defects typically far exceed the time saved by cutting validation corners.
Organizations must establish realistic timelines that accommodate thorough validation while still maintaining competitive delivery velocity. This balance requires honest conversations about quality expectations, acceptable risk levels, and the true cost of validation shortcuts.
💡 Practical Implementation Roadmap
Transforming validation practices doesn’t happen overnight. Teams need practical roadmaps that deliver incremental improvements while building toward comprehensive checkpoint frameworks.
Assessment and Gap Identification
Begin by honestly assessing current validation practices to identify specific gaps and weaknesses. Review recent production incidents to determine which would have been caught by better validation checkpoints. Analyze existing test coverage to find scenarios and integration points that lack adequate validation.
This assessment creates a baseline for measuring improvement and helps prioritize which validation enhancements will deliver the greatest risk reduction for the effort invested.
Incremental Framework Development
Rather than attempting comprehensive validation transformation immediately, implement checkpoint improvements incrementally. Start with the highest-risk areas or most frequent failure points, then systematically expand validation coverage over time.
This incremental approach delivers value quickly, maintains team morale through visible progress, and allows learning from early implementation experiences before committing to organization-wide frameworks.
Continuous Refinement and Learning
Validation checkpoint frameworks should evolve based on actual results and changing application characteristics. Regularly review which checkpoints effectively catch issues, which prove redundant, and where new validation gaps emerge as applications evolve.
This continuous refinement keeps validation frameworks relevant and efficient rather than allowing them to ossify into bureaucratic checkbox exercises that consume resources without delivering proportional quality benefits.

🎯 Achieving Validation Mastery
Mastering validation checkpoints transforms quality assurance from reactive firefighting into proactive issue prevention. Teams that implement comprehensive checkpoint frameworks catch problems early when fixes are simple, prevent defects from reaching users, and build confidence that releases will function as intended.
The journey toward validation excellence requires commitment to systematic approaches, investment in appropriate automation, cultivation of testing expertise, and organizational cultures that value thorough validation. Teams that make these investments discover that comprehensive validation accelerates development by reducing rework and eliminating the disruptions caused by production incidents.
Start by examining your current validation practices with honest eyes. Identify the gaps, implement targeted improvements, and build progressively toward validation frameworks that provide true confidence in software quality. The path to flawless results begins with recognizing that incomplete testing represents not just a quality risk but an opportunity for competitive advantage through superior reliability.
Your users may never know about the exhaustive validation checkpoints that prevented issues they never experienced, but that invisible excellence defines the difference between adequate software and truly exceptional applications that consistently deliver value without disruption.
Toni Santos is a data visualization analyst and cognitive systems researcher specializing in the study of interpretation limits, decision support frameworks, and the risks of error amplification in visual data systems. Through an interdisciplinary and analytically-focused lens, Toni investigates how humans decode quantitative information, make decisions under uncertainty, and navigate complexity through manually constructed visual representations. His work is grounded in a fascination with charts not only as information displays, but as carriers of cognitive burden. From cognitive interpretation limits to error amplification and decision support effectiveness, Toni uncovers the perceptual and cognitive tools through which users extract meaning from manually constructed visualizations. With a background in visual analytics and cognitive science, Toni blends perceptual analysis with empirical research to reveal how charts influence judgment, transmit insight, and encode decision-critical knowledge. As the creative mind behind xyvarions, Toni curates illustrated methodologies, interpretive chart studies, and cognitive frameworks that examine the deep analytical ties between visualization, interpretation, and manual construction techniques. His work is a tribute to: The perceptual challenges of Cognitive Interpretation Limits The strategic value of Decision Support Effectiveness The cascading dangers of Error Amplification Risks The deliberate craft of Manual Chart Construction Whether you're a visualization practitioner, cognitive researcher, or curious explorer of analytical clarity, Toni invites you to explore the hidden mechanics of chart interpretation — one axis, one mark, one decision at a time.